For the #Azure Database for PostgreSQL Flexible server, data encryption with customer-managed passwords is configured at the server level. The data encryption key for the service is encrypted for a specific server using a customer-managed secret known as the key encryption key (KEK). (DEK). An encrypted key called the KEK is kept in a customer-owned and customer-managed system Azure Key Vault
Benefits
Data encryption with customer-managed keys for Azure Database for PostgreSQL – Flexible Server provides the following benefits:
- You fully control data-access by the ability to remove the key and make the database inaccessible.
- Full control over the key-lifecycle, including rotation of the key to aligning with corporate policies.
- Central management and organization of keys in Azure Key Vault.
- Enabling encryption doesn’t have any additional performance impact with or without customers managed key (CMK) as PostgreSQL relies on the Azure storage layer for data encryption in both scenarios. The only difference is when CMK is used Azure Storage Encryption Key, which performs actual data encryption, is encrypted using CMK.
- Ability to implement separation of duties between security officers, DBA, and system administrators.
Data encryption with a customer-managed key work
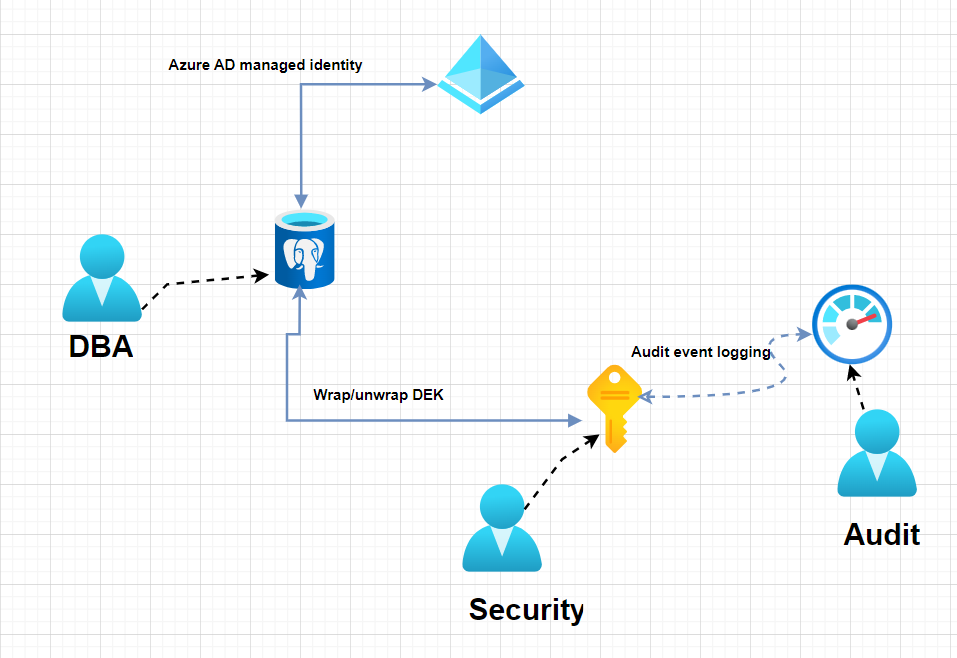
In order for a PostgreSQL server to encrypt the DEK using client-managed keys kept in Key Vault, the server needs to have the following access privileges granted by Key Vault administrator:
get: The key’s characteristics and public portion can be retrieved from the key vault.
list: For listing\iterating through keys in, the key Vault.
Wrapkey: To be able to encrypt the DEK. The encrypted DEK is stored in the Azure Database for PostgreSQL.
unwrapkey: To be able to decrypt the DEK. Azure Database for PostgreSQL needs the decrypted DEK to encrypt/decrypt the data
When you’re using data encryption by using a customer-managed key, here are recommendations for configuring Key Vault:
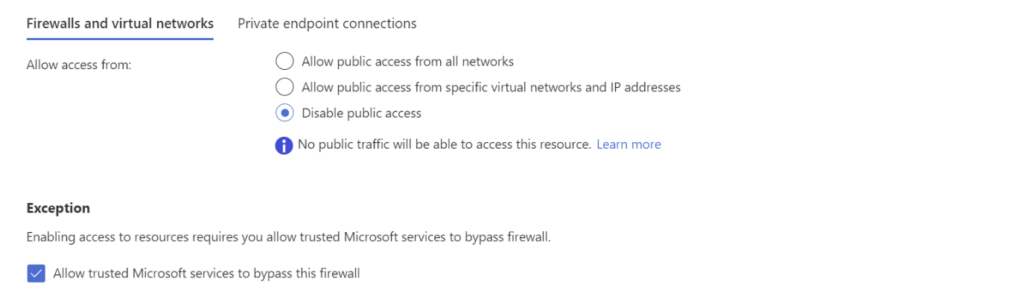
Lock down the Azure KeyVault to only disable public access and allow only trusted Microsoft services to secure the resources.
more details- Data Encryption with a Customer-managed Key