An app registration with the Microsoft identity platform can be generated automatically by the Container Apps Authentication feature. A registration that you or a directory administrator generates independently may also be used.
Below is the two options:
Create a new app registration automatically
Use an existing registration created separately
Configure your container app to use Azure Active Directory
- Go to Azure portal and naviagte to your app
- On the left menu, select Authentication and select Add identity provider
- From the dropdown, select Microsoft in the identity provider
- For app registration, you can choose to use an existing registration from this directory, which will automatically gather the necessary app information. If you aren’t registered with the app, or your registration isn’t from an existing tenant, you can provide the details of an existing app registration.
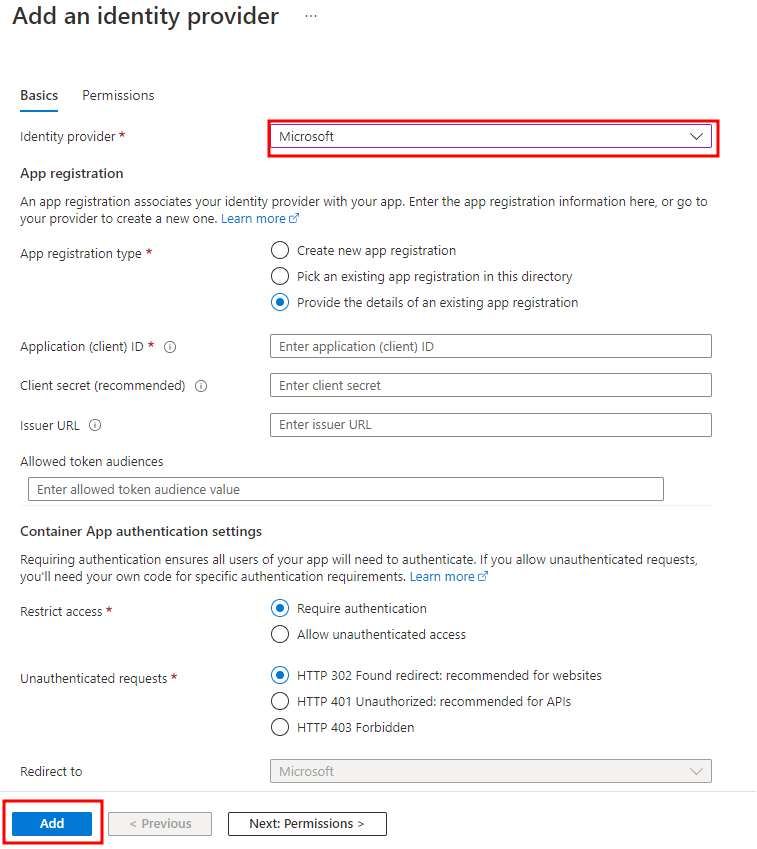
- If this is the first identity provider configured for the application, you will be asked to configure authentication settings for Container Apps. Otherwise, you can proceed to the next step.
- Select Add.
Ensure that your container app can be accessed by client app
Your container app was registered so that users could be verified. This section explains how to set up native client or daemon apps so they can make requests for users or themselves to access the APIs exposed by your container app. If all you want to do is authenticate users, you don’t need to finish the procedures in this section.
Native client application
Native clients can be registered to request access to your container app’s APIs on behalf of logged in users.
- Go to Azure portal, select Active Directory > App registrations > New registration.
- In the Register an application page, enter a Name for your app registration.
- In the Redirect URI, select Public client (mobile & desktop) and type the URL
<app-url>/.auth/login/aad/callback. For example,https://<hostname>.azurecontainerapps.io/.auth/login/aad/callback. NoteFor a Microsoft Store application, use the package SID as the URI instead. - Select Register.
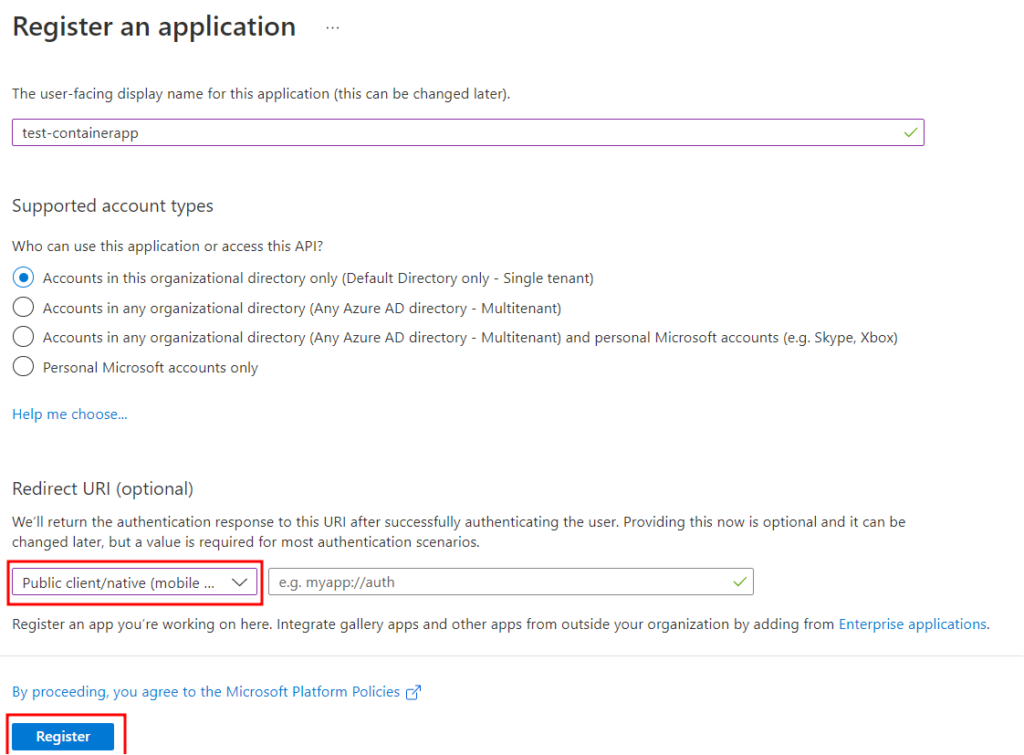
- After the app registration is created, copy the value of Application (client) ID.
- Select API permissions > Add a permission > My APIs.
- Select the app registration you created earlier for your container app. If you don’t see the app registration, make sure that you’ve added the user_impersonation scope in Create an app registration in Azure AD for your container app.
- Under Delegated permissions, select user_impersonation, and then select Add permissions.
Your native client application now has the ability to request access to your container app on behalf of a user.