You can deploy a Citrix ADC VPX standalone instance on AWS by using the following options:
- AWS web console
- Citrix-authored CloudFormation template
- AWS CLI
This topic describes the procedure for deploying a Citrix ADC VPX instance on AWS.
Before you start your deployment, read the following topics:
Deploy a Citrix ADC VPX instance on AWS by using the AWS web console
You can deploy a Citrix ADC VPX instance on AWS through the AWS web console. The deployment process includes the following steps:
- Create a Key Pair
- Create a Virtual Private Cloud (VPC)
- Add more subnets
- Create security groups and security rules
- Add route tables
- Create an internet gateway
- Create a Citrix ADC VPX instance
- Create and attach more network interfaces
- Attach elastic IPs to the management NIC
- Connect to the VPX instance
Step 1: Create a key pair.
Amazon EC2 uses a key pair to encrypt and decrypt logon information. To log on to your instance, you must create a key pair, specify the name of the key pair when you launch the instance, and provide the private key when you connect to the instance.
When you review and launch an instance by using the AWS Launch Instance wizard, you are prompted to use an existing key pair or create a new key pair. More more information about how to create a key pair, see Amazon EC2 Key Pairs.
Step 2: Create a VPC.
A Citrix ADC VPC instance is deployed inside an AWS VPC. A VPC allows you to define the virtual network dedicated to your AWS account. For more information about AWS VPC, see Getting Started With Amazon VPC.
While creating a VPC for your Citrix ADC VPX instance, keep the following points in mind.
- Use the VPC with a Single Public Subnet Only option to create an AWS VPC in an AWS availability zone.
- Citrix recommends that you create at least three subnets, of the following types:
- One subnet for management traffic. You place the management IP(NSIP) on this subnet. By default elastic network interface (ENI) eth0 is used for management IP.
- One or more subnets for client-access (user-to-Citrix ADC VPX) traffic, through which clients connect to one or more virtual IP (VIP) addresses assigned to Citrix ADC load balancing virtual servers.
- One or more subnets for the server-access (VPX-to-server) traffic, through which your servers connect to VPX-owned subnet IP (SNIP) addresses. For more information about Citrix ADC load balancing and virtual servers, virtual IP addresses (VIPs), and subnet IP addresses (SNIPs), see:
- All subnets must be in the same availability zone.
Step 3: Add subnets.
When you used the VPC wizard, only one subnet was created. Depending on your requirement, you might want to create more subnets. For more information about how to create more subnets, see Adding a Subnet to Your VPC.
Step 4: Create security groups and security rules.
To control inbound and outbound traffic, create security groups and add rules to the groups. For more information how to create groups and add rules, see Security Groups for Your VPC.
Port 22, 80, 443 to be opened on the Security group for SSH, HTTP, and HTTPS access respectively.
Step 5: Add route tables.
Route table contains a set of rules, called routes, that are used to determine where network traffic is directed. Each subnet in your VPC must be associated with a route table. For more information about how to create a route table, see Route Tables.
Step 6: Create an internet gateway.
An internet gateway serves two purposes: to provide a target in your VPC route tables for internet-routable traffic, and to perform network address translation (NAT) for instances that have been assigned public IPv4 addresses.
Create an internet gateway for internet traffic. For more information about how to create an Internet Gateway, see the section Attaching an Internet Gateway.
Step 7: Create a Citrix ADC VPX instance by using the AWS EC2 service.
To create a Citrix ADC VPX instance by using the AWS EC2 service, complete the following steps.
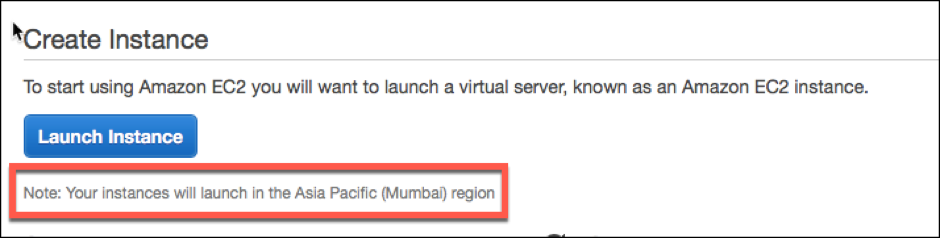
- From the AWS dashboard, go to Compute > EC2 > Launch Instance > AWS Marketplace.Before you click Launch Instance, ensure your region is correct by checking the note that appears under Launch Instance.
- In the Search AWS Marketplace bar, search with the keyword Citrix ADC VPX.
- Select the version you want to deploy and then click Select. For the Citrix ADC VPX version, you have the following options:
- A licensed version
- Citrix ADC VPX Express appliance (This is a free virtual appliance, which is available from Citrix ADC 12.0 56.20.)
- Bring your own device
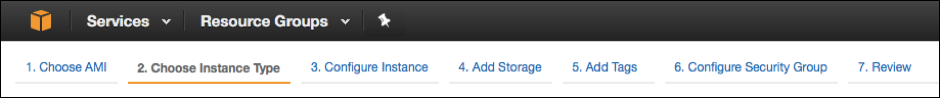
The Launch Instance wizard starts. Follow the wizard to create an instance. The wizard prompts you to:
- Choose Instance Type
- Configure Instance
- Add Storage
- Add Tags
- Configure Security Group
- Review
Step 8: Create and attach more network interfaces.
Create two more network interfaces for VIP and SNIP. For more information about how to create more network interfaces, see the Creating a Network Interface section.
After you’ve created the network interfaces, you must attach them to the VPX instance. Before attaching the interface, shut down the VPX instance, attach the interface, and power on the instance. For more information about how to attach network interfaces, see the Attaching a Network Interface When Launching an Instance section.
Step 9: Allocate and associate elastic IPs.
If you assign a public IP address to an EC2 instance, it remains assigned only until the instance is stopped. After that, the address is released back to the pool. When you restart the instance, a new public IP address is assigned.
In contrast, an elastic IP (EIP) address remains assigned until the address is disassociated from an instance.
Allocate and associate an elastic IP for the management NIC. For more information about how to allocate and associate elastic IP addresses, see these topics:
These steps complete the procedure to create a Citrix ADC VPX instance on AWS. It can take a few minutes for the instance to be ready. Check that your instance has passed its status checks. You can view this information in the Status Checks column on the Instances page.
Step 10: Connect to the VPX instance.
After you’ve created the VPX instance, you connect the instance by using the GUI and an SSH client.
- GUI
The following are the default administrator credentials to access a Citrix ADC VPX instance
User name: nsroot
Password: The default password for the ns root account is set to the AWS instance-ID of the Citrix ADC VPX instance. On your first logon, you are prompted to change the password for security reasons. After changing the password, you must save the configuration. If the configuration is not saved and the instance restarts, you must log on with the default password. Change the password again at the prompt.
- SSH client
From the AWS management console, select the Citrix ADC VPX instance and click Connect. Follow the instructions given on the Connect to Your Instance page.
For more information about how to deploy a Citrix ADC VPX standalone instance on AWS by using the AWS web console, see:
- Scenario: standalone instance
- How to configure a Citrix NetScaler VPX instance on AWS by using Citrix CloudFormation template
Configure a Citrix ADC VPX instance by using the Citrix CloudFormation template
You can use the Citrix-provided CloudFormation template to automate VPX instance launch. The template provides functionality to launch a single Citrix ADC VPX instance, or to create a high availability environment with a pair of Citrix ADC VPX instances.
You can launch the template from AWS Marketplace or GitHub.
The CloudFormation template requires an existing VPC environment, and it launches a VPX instance with three elastic network interfaces (ENIs). Before you start the CloudFormation template, ensure that you complete the following requirements:
- An AWS virtual private cloud (VPC)
- Three subnets within the VPC: one for management, one for client traffic, and one for back-end servers
- An EC2 key pair to enable SSH access to the instance
- A security group with UDP 3003, TCP 3009–3010, HTTP, SSH ports open